 |
|

 |
|

CyLock MFA enables strong Multi-Factor Authentication for any firewall based SSL VPN user login. CyLock MFA integrates with the firewall through CyLock MFA RADIUS proxy component installed in a server within the organization’s local network.
The CyLock MFA RADIUS proxy component enables any firewall with RADIUS protocol support to carry out a strong Multi-Factor Authentication (MFA) during remote login to remote network through SSL VPN.
Firewall Devices: Sonicwall NSa series, NSsp series, Nsv series, TZ series, SOHO series supports RADIUS authentication.
CyLock MFA RADIUS proxy component needs to be installed within your network to enable MFA during SSL VPN login process. First factors (user login credentials) can be authenticated with an on-premise AD / LDAP / LDAP or against CyLock MFA local store. A typical deployment architecture and process is shown below.
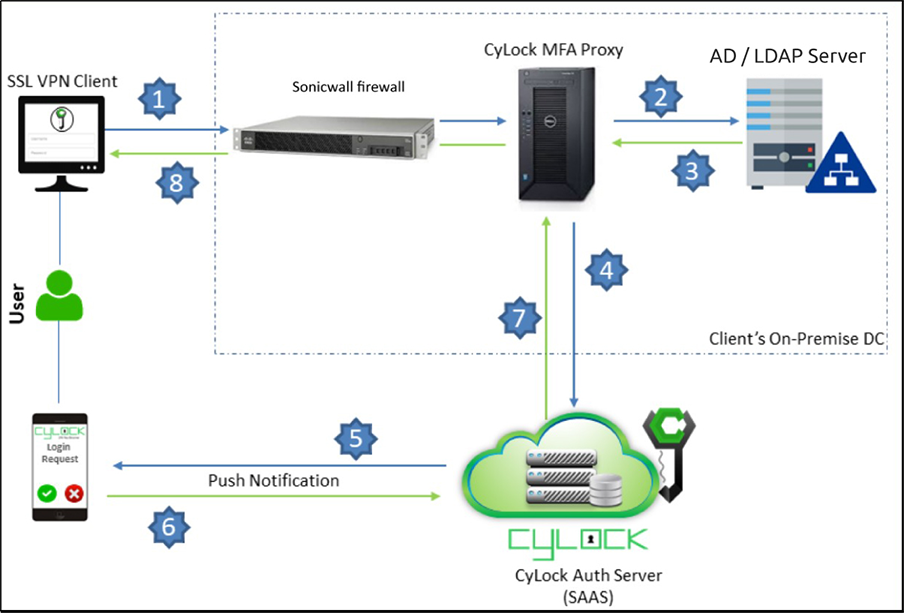
Figure 1 – Deployment Architecture Block diagram of integrating Sonicwall Firewall with CyLock RADIUS Proxy
Note:
CyLock MFA RADIUS Proxy component will receive incoming RADIUS requests from your firewall during SSL VPN login. The proxy component will then perform the primary authentication (first factor authentication) either with your internal AD / LDAP Server / LDAP Server or CyLock MFA local store, and then contact CyLock MFA Auth Server for second factor authentication.
CyLock MFA RADIUS Proxy can be installed on a physical or virtual host within your network. We recommend a system with at least 4 vCPU, 200 MB disk space, and 4 GB RAM. CyLock MFA RADIUS Proxy supports the following operating systems:
Install Node.JS in the server where the CyLock MFA RADIUS Proxy component will be installed.
Download the CyLock MFA RADIUS Proxy component. Refer Prerequisites section above. After downloading, copy/move the Proxy Component to the respective server.
Go to the folder where the Proxy component has been copied. Extract the CyLock_radius_proxy.zip. After extracting, follow the below steps to configure the component.
On Windows or Linux machine go to the respective folder where the proxy component was copied & extracted.
Open the cyconfig.js file in CyRadius Folder with administrative privileges and edit the following properties:
| # | Property Name (key) | Description (value) |
|---|---|---|
| 1 | url |
Enter Auth URL (Ex - https://demoauth.cybernexa.com/api/v2/srv/) |
| 2 | id_sp | Customer ID value. Refer point #4 in Prerequisites section. |
| 3 | Authorization | API Key value. Refer point #4 in Prerequisites section. |
| 4 | radius_secret | Enter the encrypted RADIUS secret key. To obtain encrypted secret key please refer ‘Key Encryption Process’ section. |
Note: Do not modify the key in the key-value pair.
To enable RADIUS Proxy component, communicate with MS AD / LDAP server or LDAP server, configure the adconfig.js file.
Open the adconfig.js file in CyRadius Folder with administrative privileges and edit the following properties.
| # | Property Name (key) | Description (value) |
|---|---|---|
| 1 | Open_ldap_server | Enter your open ldap server URL (ex: ldaps://ldap.cybernexa.com) |
| 2 | domain | Provide your AD / LDAP domain name. |
| 3 | url | For secured LDAP: ldaps://computername.domain.com or else simply use For normal LDAP: ldap://computername.domain.com |
| 4 | baseDN | AD / LDAP Domain name |
| 5 | Password | AD / LDAP server Administrator user’s encrypted password. To obtain the encrypted AD/LDAP Password please refer ‘Key encryption Process’ section. |
Note: Do not modify the key in the key-value pair.
Encrypting Radius Secret Key and AD / LDAP Password.
a. After Unzip the radius_proxy.zip file. Go to the secure_cred directory and execute the "secure_cred.js" file using the command below
(i).node secure_cred.js
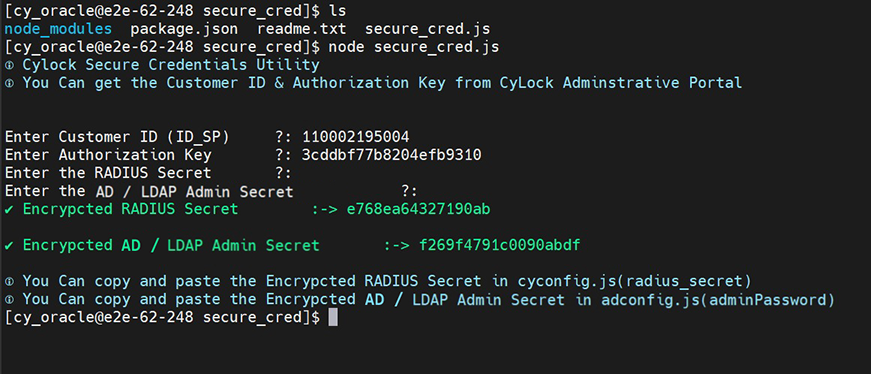
Figure 2 – RADIUS and LDAP Admin Secret key encryption
You can copy and paste the Encrypted RADIUS Secret in cyconfig.js on radius_secret parameter.
You can copy and paste the Encrypted AD / LDAP Admin Secret in adconfig.js on password parameter.
Note:The RADIUS secret and AD / LDAP Passwords should always be encrypted.
To start the component automatically create and run as service
For creating service file follow the below steps:
//*****Start of the file*****
[Unit]
Description=cylockradiusservice
After=syslog.target
After=network.target[Service]
User=cylock_iam
//Replace with your system user name
Type=simple
[Service]
Restart=always
StandardOutput=syslog
StandardError=syslog
//Provide the path of the CyLock MFA RADIUS proxy component (server.js)
WorkingDirectory=/home/cylock_iam/package/
//Provide the path of the CyLock MFA RADIUS proxy component (server.js)
ExecStart=/usr/bin/node /home/cylock_iam/package/server.js
SyslogIdentifier=cylockradiusservice
[Install]
1.WantedBy=multi-user.target
//******End of the file******
a.:wq!
a.systemctl enable cylockradiusservice.service
a.systemctl start cylockradiusservice.service
Note:For Windows OS, create a service for the batch file (.bat) using nssm.exe utility and start the service.
CyLock MFA integrates with your firewall device based VPN via RADIUS to add Multi-Factor Authentication (MFA) to SSL VPN login. In this context your firewall device will act as RADIUS client and the CyLock MFA RADIUS Proxy component as the RADIUS server.
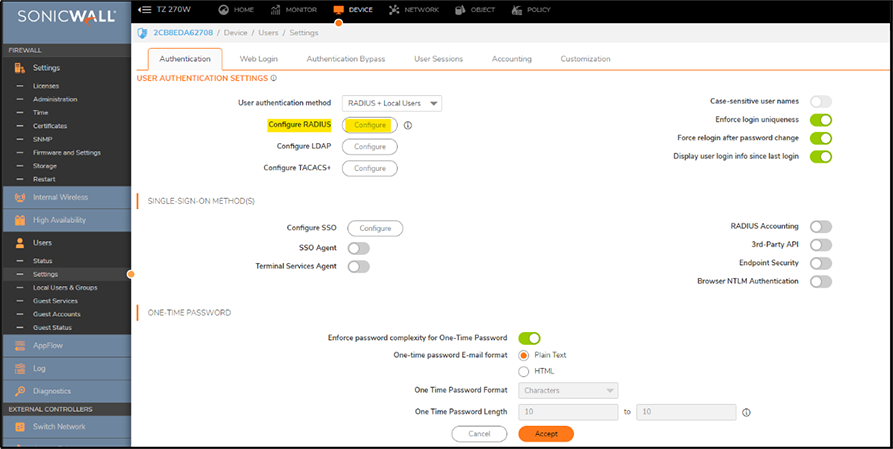
Figure 3 – SonicWall Management interface - Adding Radius server
Note:The Shared Secret has to be identical to the one entered in the RADIUS Client in IAS.
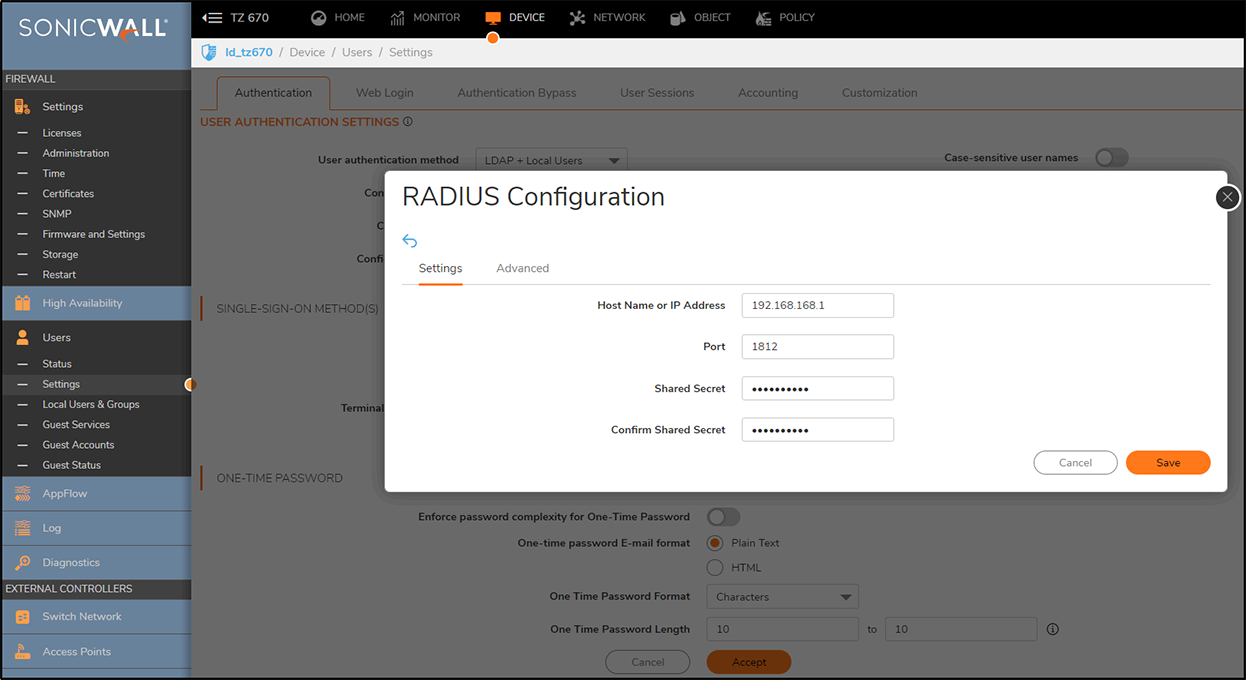
Figure 4 – Entering Radius Server ip, port number and secret key
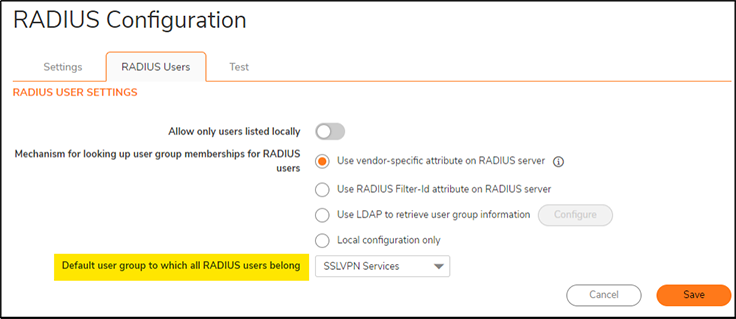
Figure 5 – Choosing default user group to which all RADIUS users belong
In this example, the local users belong to SSLVPN Service user group, and they will be asked to do CyLock MFA in RADIUS when a VPN SSL connection is required.
Types of Authentication Options:
CyLock MFA allows the following Authentication options to login SSL VPN.
| # | Mode | Process Steps |
|---|---|---|
| 1 | Default Mode | In password field enter << Your password >> (for carrying out the default authentication) |
| 2 | Online | In password field enter << Your password >>,1 (for carrying Online MFA Push authentication) |
| 3 | Online | In password field enter << Your password >>,2 (for carrying Online MFA Push+PIN authentication) |
| 4 | Online | In password field enter << Your password >>,3 (for carrying Online MFA Push+Bio authentication) |
| 5 | Offline (CR-OTP - Display) | In password field enter << Your password >>,4 (for carrying Offline MFA CR-OTP (Display) authentication) |
| 6 | Offline (CR-OTP – Email) | In password field enter << Your password >>,5 (for carrying out Offline MFA CR-OTP (Email) authentication) |
| 7 | Offline (CR-OTP – SMS) | In password field enter << Your password >>,6 (for carrying Offline MFA CR-OTP (SMS) authentication) |
| 8 | Offline (POTP - Email) | In password field enter << Your password >>,7 (for carrying out Offline MFA POTP (Email) authentication) |
| 9 | Offline (POTP – SMS) | In password field enter << Your password >>,8 (for carrying Offline MFA POTP (SMS) authentication) |
| 10 | Offline (TOTP) | In password field enter << Your password >>,9 (for carrying Offline MFA TOTP authentication) |
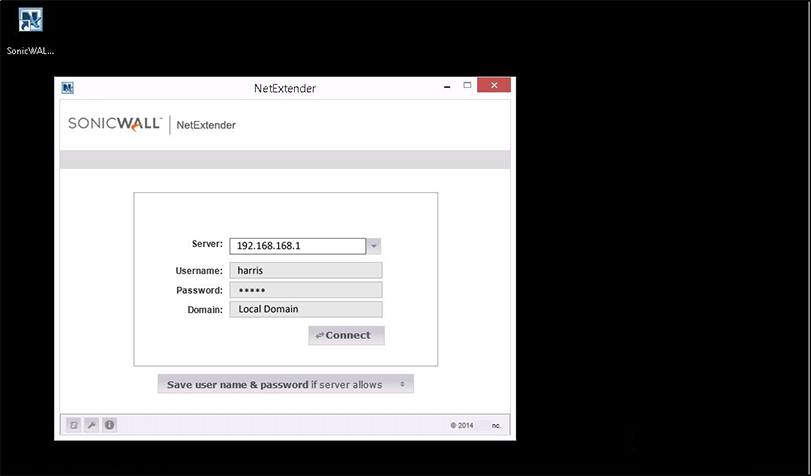
Figure 6 – Connecting to Sonicwall VPN using NetExtender VPN client
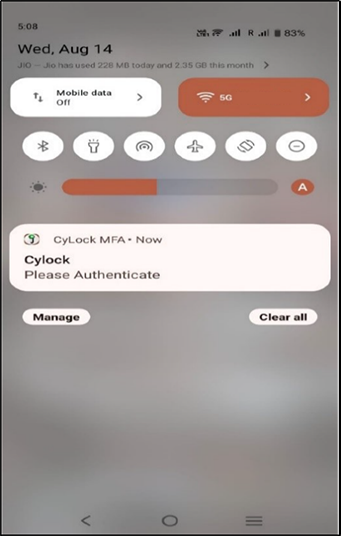
Figure 7: Push notification received in mobile
.png)
Figure 8: PUSH+PIN Authentication triggered (2FA)
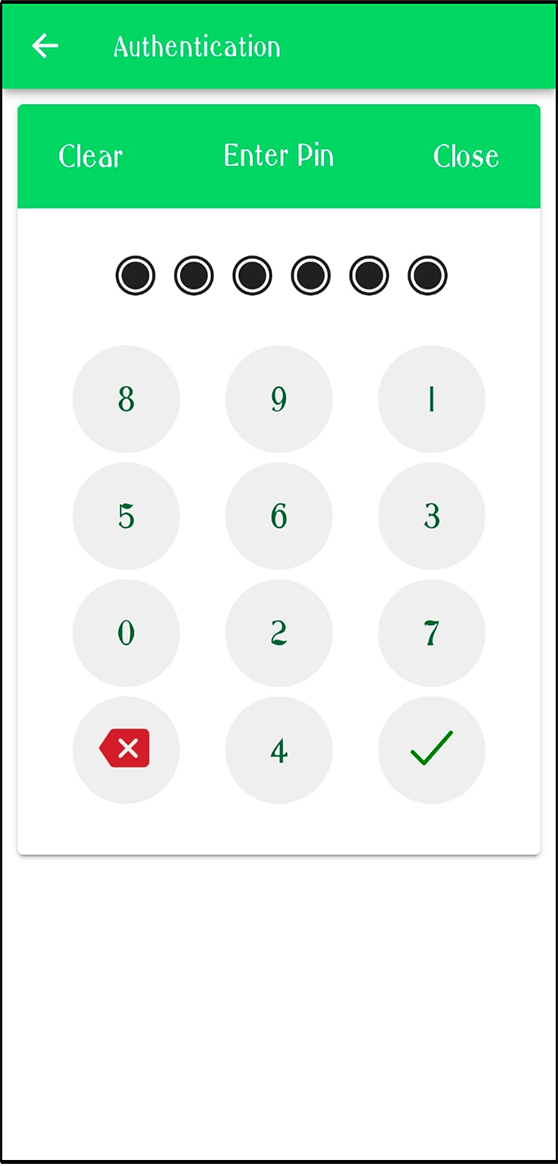
Figure 9: Entering 6 digit PIN
Once 2FA is verified user can connect to SonicWall SSL VPN Successfully.
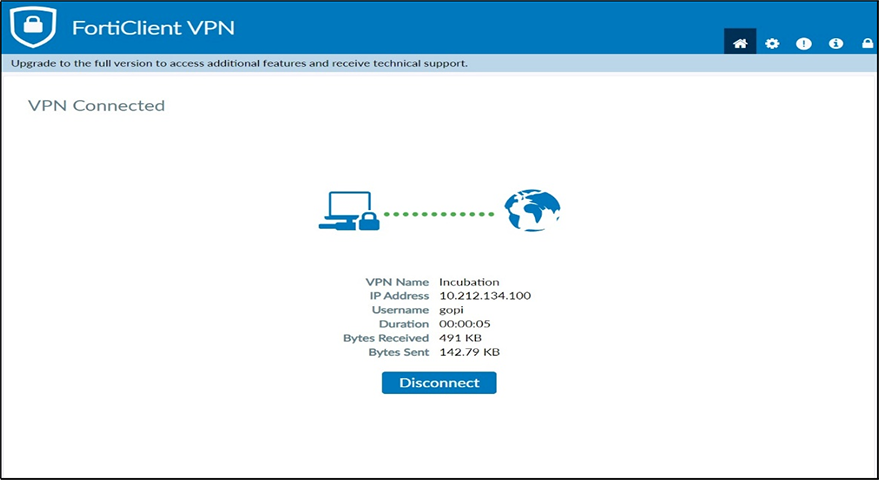
Figure 10: User connected to VPN Successfully